
Script kiddies, skiddies, kiddies, or skids are individuals who lack advanced technical knowledge or skills but use pre-existing automated tools and scripts to launch simple cyberattacks or defacements, often for the purpose of achieving recognition or causing mischief.

They are considered the lowest level of hackers, and their actions can range from annoying pranks to potentially damaging attacks. Script kiddies rely heavily on pre-made software tools, known as exploit kits[1], that automate the process of finding and exploiting vulnerabilities in target systems. These kits can be easily obtained on the internet and often require little to no coding knowledge to use. As a result, script kiddies can launch attacks with relative ease and little effort.
The more immature but unfortunately often just as dangerous exploiter of security lapses on the Internet. The typical script kiddy uses existing and frequently well known and easy-to-find techniques and programs or scripts to search for and exploit weaknesses in other computers on the Internet—often randomly and with little regard or perhaps even understanding of the potentially harmful consequences.
Carnegie Mellon report prepared for the U.K. Department of Defense in 2000
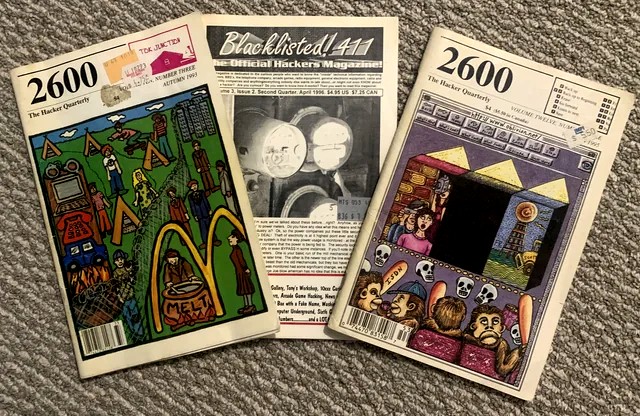
The term script kiddie first appeared in hacker zines, blogs, message boards, and Internet Relay Chat[2] in the mid-1990s. It was used to describe people who downloaded a tool without knowing or caring how it worked.
- 1993. Terms such as k0deZ kiddies appeared on an internet message board called Yabbs.
- 1996. According to the hacker blog LiveOverflow, the term script kiddie appeared in the comments of a Unix exploit.
- 1998. The hacking zine Phrack made reference to “script kiddie behavior” in one of its articles.

The motivations of script kiddies vary widely. Some are looking for a thrill or a sense of power, while others may have more malicious intentions, such as stealing personal information or causing financial harm. Script kiddies are also known for their love of attention and may launch attacks for the purpose of gaining notoriety among other hackers or within online communities.
Hackers and script kiddies differ in three areas:
- Level of experience. Script kiddies are less experienced with cybersecurity exploits than real hackers. They generally cannot write exploits or scripts on their own, so they use programs written by other people and found on the internet.
- Skills. Script kiddies have less developed hacking skills than more advanced, well-organized threat actors. As a result, they often use attacks that are easier to perform. They may prepare less for an attack, doing little research before launching it. They are also more likely to give up if their easy exploit doesn’t work in the first few tries. Experienced hackers have the programming and computer networking knowledge to adapt their attacks to dynamic internet security defenses. They can interpret a situation and adapt to new scenarios.
- Intent. Script kiddies are more likely to perform exploits for personal acclaim or to troll. They don’t always understand the tools they use and pay less attention to the consequences of hacking. A hacker will take pride in the quality of an attack, such as leaving no trace of an intrusion, for example. Most experienced threat attackers understand the consequences and ethics of what they do. By comparison, a script kiddie often focuses on quantity, seeing the number of attacks that can be mounted to get attention and notoriety.

Despite their relative lack of technical skill, script kiddies can still pose a threat to individuals and organizations. By exploiting known vulnerabilities in software and systems, they can potentially cause damage or steal sensitive information. Additionally, their attacks can serve as a gateway for more skilled hackers to gain access to systems.
A script kiddie attack is characterized by:
- Repeatability. A script kiddie uses a pre-made attack that’s probably been used on other companies at different times.
- Openness. Script kiddies don’t know how to mask attacks, so you probably notice the problem right away.
- Unsophisticated. Script kiddies often can’t cover their tracks, so you may be able to identify who they are and where they come from very quickly.
- Impulsivity. These novice hackers rarely understand what their scripts will do and how they work. They’re willing to try the code anyway.

To protect against script kiddie attacks, individuals and organizations should take basic cybersecurity measures such as keeping software up to date, using strong passwords, and limiting access to sensitive information. Additionally, organizations should consider implementing more advanced security measures such as intrusion detection systems and firewalls.
In October 2015, TalkTalk Telecom Group PLC, a UK-based telecom company, experienced a major hack and subsequent data breach that affected millions of customers. The attack resulted in the theft of sensitive customer information, including names, addresses, dates of birth, and bank details. An unnamed 15-year-old boy was arrested in connection with the attack. The boy, who was from Northern Ireland, was arrested on suspicion of Computer Misuse Act offenses and later released on bail. The boy was identified as the suspect after a joint investigation by the UK’s Metropolitan Police Cyber Crime Unit and the Police Service of Northern Ireland. The attack was initially thought to have been carried out by a group of hackers, but it was later revealed that the 15-year-old boy had acted alone. He reportedly used a well-known hacking tool called SQLMap to exploit a vulnerability in TalkTalk’s website and gain access to customer data. The boy was charged with several offenses, including unauthorized access to computer material and supplying an article for use in an offense. In November 2016, he pleaded guilty to seven offenses and was sentenced to a 12-month rehabilitation order and a three-year youth rehabilitation order. The TalkTalk data breach highlighted the vulnerability of companies and individuals to cyberattacks and the importance of taking steps to protect sensitive information. The incident led to increased scrutiny of TalkTalk’s security practices and highlighted the need for companies to prioritize cybersecurity measures.

Footnotes
- Software tools are available on the internet that can be used by script kiddies to launch attacks without much technical knowledge or skill. These tools include automated exploit kits that scan systems for vulnerabilities and attempt to exploit them, as well as password-cracking tools that can be used to brute-force login credentials. Other popular tools include denial-of-service (DoS) attack tools, which can be used to flood a target system with traffic and cause it to become unresponsive, and remote access tools, which can be used to take control of a compromised system. While some of these tools may have legitimate uses in certain contexts, they are often used by script kiddies for malicious purposes. [Back]
- Internet Relay Chat (IRC) is a real-time communication protocol that enables users to connect to chat rooms and communicate with others around the world. IRC was first developed in 1988 and became popular in the 1990s as a means of online chat and socialization. Today, IRC is still used by many communities and organizations, particularly in the open-source software community. Users can connect to IRC servers using client software, such as mIRC or HexChat, and can join different channels to chat with others on a wide range of topics. [Back]
Further Reading
Sources
- Newspapers
- “Script Kiddie” Wikipedia
- “Script Kiddie: Unskilled Amateur or Dangerous Hackers?” United States Cybersecurity Magazine
- “What is a script kiddie?” TechTarget
- “Script Kiddies and Skiddies: Identifying Unskilled Hackers” okta
- “15-year-old script kiddie arrested in TalkTalk hacking investigation” siliconAngle
- “Script Kiddies – Case Study” Cyber.UK
- “Script Kiddie.” TechTarget, Searchhttps://cyber.uk/areas-of-cyber-security/cyber-security-threat-groups-2/script-kiddies-case-study/Security. https://searchsecurity.techtarget.com/definition/script-kiddie
- “What is a Script Kiddie?” Norton, https://us.norton.com/internetsecurity-how-to-what-is-a-script-kiddie.html
- “The rise of the script kiddie: Why low-skilled cyber attacks are on the rise.” ZDNet, https://www.zdnet.com/article/the-rise-of-the-script-kiddie-why-low-skilled-cyber-attacks-are-on-the-rise/
- “IRC – Internet Relay Chat.” IRChelp.org, https://www.irchelp.org/irchelp/new2irc.html
- “What is IRC?” Lifewire, https://www.lifewire.com/what-is-irc-2483594
- “IRC: What is it and why do people still use it?” Network World, https://www.networkworld.com/article/3259464/irc-what-is-it-and-why-do-people-still-use-it.html
- “The rise of the script kiddie: Why low-skilled cyber attacks are on the rise.” ZDNet, https://www.zdnet.com/article/the-rise-of-the-script-kiddie-why-low-skilled-cyber-attacks-are-on-the-rise/
- “What are the most popular hacking tools?” CSO Online, https://www.csoonline.com/article/3303817/what-are-the-most-popular-hacking-tools.html




